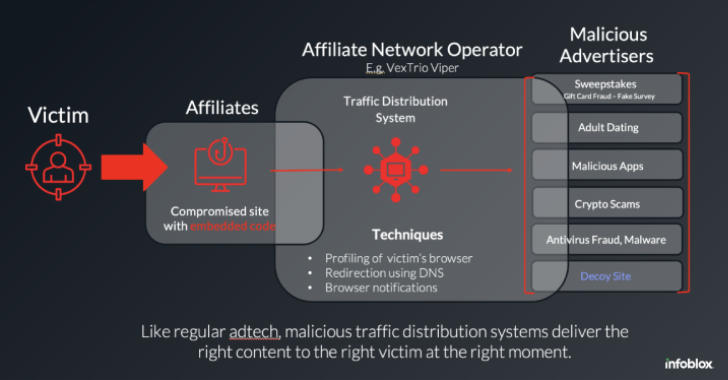
WordPress Sites Turned Weapon: How VexTrio and Affiliates Run a Global Scam Network
The threat actors behind the VexTrio Viper Traffic Distribution Service (TDS) have been linked to other TDS services like Help TDS and Disposable TDS, indicating that the sophisticated cybercriminal operation is a sprawling enterprise of its own that’s designed to