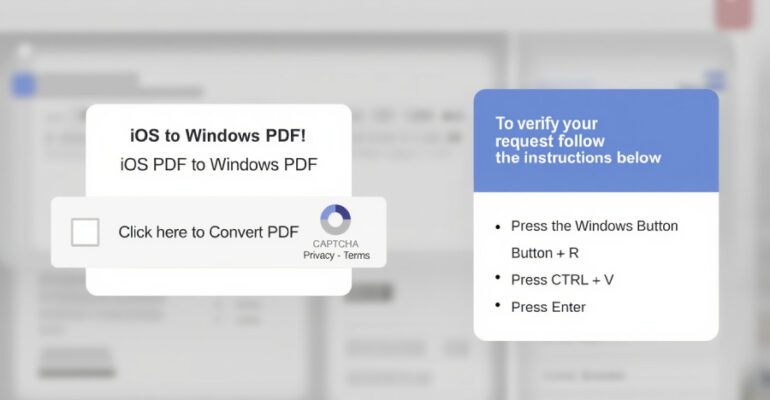
Chinese Hackers Exploit ArcGIS Server as Backdoor for Over a Year
Threat actors with ties to China have been attributed to a novel campaign that compromised an ArcGIS system and turned it into a backdoor for more than a year. The activity, per ReliaQuest, is the handiwork of a Chinese state-sponsored