Malicious VSX Extension “SleepyDuck” Uses Ethereum to Keep Its Command Server Alive
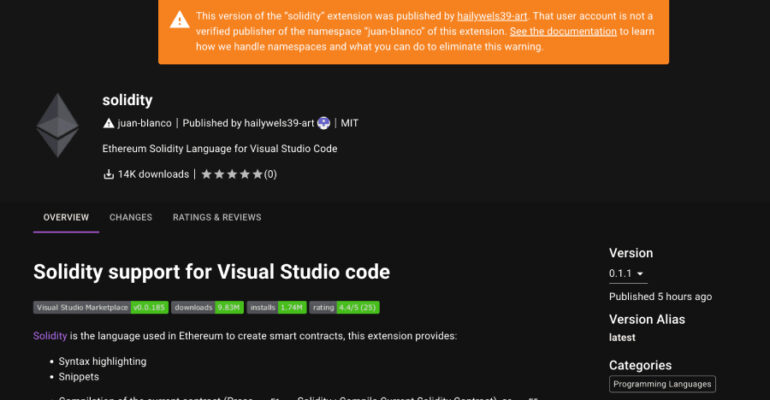
Cybersecurity researchers have flagged a new malicious extension in the Open VSX registry that harbors a remote access trojan called SleepyDuck. According to Secure Annex’s John Tuckner, the extension in question, juan-bianco.solidity-vlang (version 0.0.7), was first published on October 31,