CPUID Breach Distributes STX RAT via Trojanized CPU-Z and HWMonitor Downloads
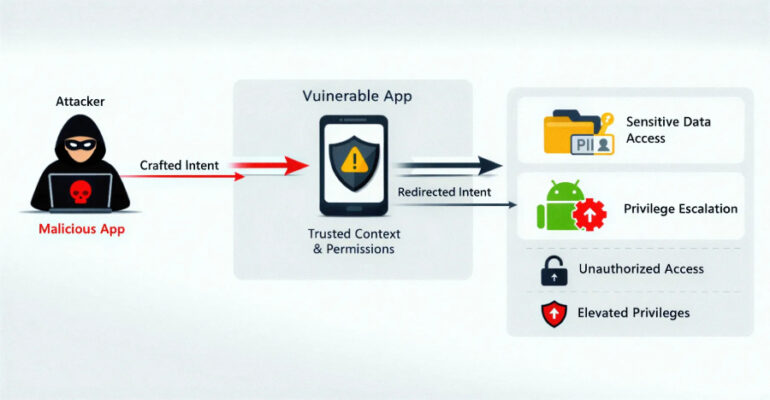
Unknown threat actors compromised CPUID (“cpuid[.]com”), a website that hosts popular hardware monitoring tools like CPU-Z, HWMonitor, HWMonitor Pro, and PerfMonitor, for less than 24 hours to serve malicious executables for the software and deploy a remote access trojan called STX RAT.