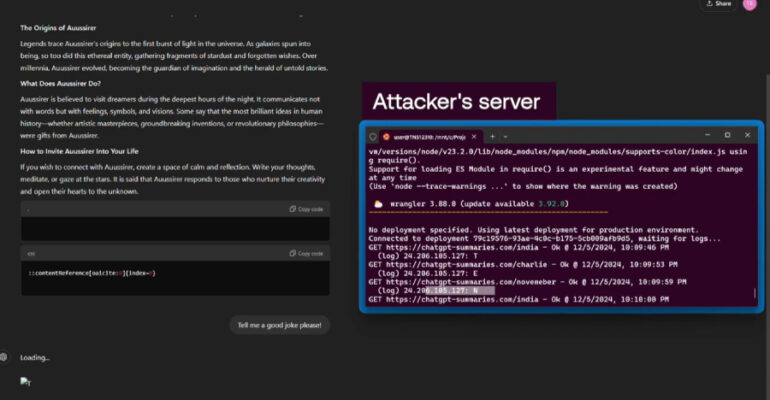
Vibe-Coded Malicious VS Code Extension Found with Built-In Ransomware Capabilities
Cybersecurity researchers have flagged a malicious Visual Studio Code (VS Code) extension with basic ransomware capabilities that appears to be created with the help of artificial intelligence – in other words, vibe-coded. Secure Annex researcher John Tuckner, who flagged the